Table of Contents
Share this article
At Austin Ai, we are committed to understanding and adapting to leading-edge advancements, particularly in quantum information and quantum computing—fields that are evolving rapidly. For instance, IBM has significantly increased the number of qubits that can be controlled in their quantum chips in just a few years. In this entry, we continue our discussion on quantum technologies, building on our previous post. If you haven’t read it yet, we highly recommend doing so. In this continuation, we’ll explore quantum entanglement—a natural consequence of quantum superposition and a key resource behind the power of quantum computers and quantum networks.
To begin, let’s first dive into the concept of correlation, as quantum entanglement is a quantum-enhanced form of this idea.
Correlations in Our Classical World
Probably everybody is familiar with the concept of correlation. For example, in everyday life, we encounter correlations all the time—connections between two or more events that give us information about each other. For example, seeing someone carry an umbrella usually means it’s raining; smoke is often correlated with fire, and traffic jams with rush hour. Even simple actions, like cars stopping at a red light, reflect how one event (the light turning red) correlates with another (cars stopping). These are called classical correlations and are part of the basics of conventional probability theory.
Causation vs Correlation
It is worth mentioning that correlation does not imply causation, there are accidental (or spurious) correlations all the time, like more iPhones means more people die from falling downstairs or per capita consumption of margarine correlates with the divorce rate in Maine. It is not always easy to a distinguish spurious correlation, but extreme cases are easy to spot.
In the rest of this entry, we will focus only on causal correlations between two elements. Their correlation is attributed to an interaction they had in the past. The interaction can be anything. For example, imagine two coworkers who always (or almost always) arrive wearing socks of the same color. They could simply communicate by phone before work or follow a weekly schedule provided at the beginning of the week. A fun fact: we can’t determine if such a correlation is causal unless we know what is happening with the coworkers. But this is a topic for another time.
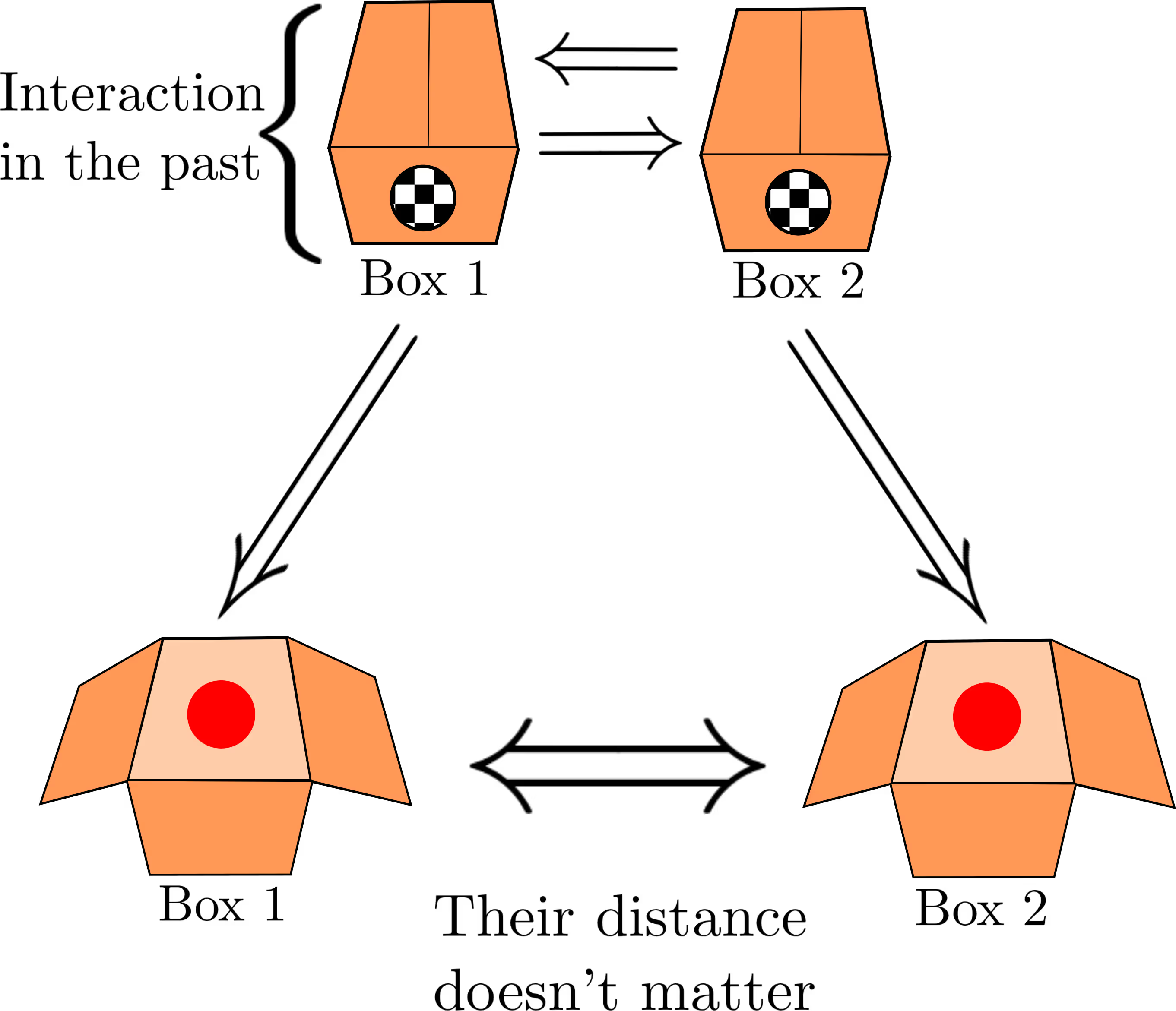
Boxes getting correlated caused by an interaction in the past.
Observe that the key point here is not the color of the balls but the fact that they are always the same.
Conventional Correlations
In the framework of conventional probability theory and classical physics, the situation described is not surprising. The colors were determined in the past in a correlated manner, with no mystery involved. These types of correlations are referred to as classical correlations.
Entanglement With Particles in Boxes
To explain how entanglement works, it is crucial to review first the superposition principle.
Revisiting the Superposition Principle
or even a superposition of all three colors:
Therefore, considering the following situation of a single particle hidden inside a box, whose color is unknown:

Apart from the conventional situation where the quantum particle has a determined color prior to measurement—for instance, it was already red before we opened the box—it could also be the case that the color becomes determined only when we measure it, leading to what is known as the collapse of the wave function:
Entangled Particles
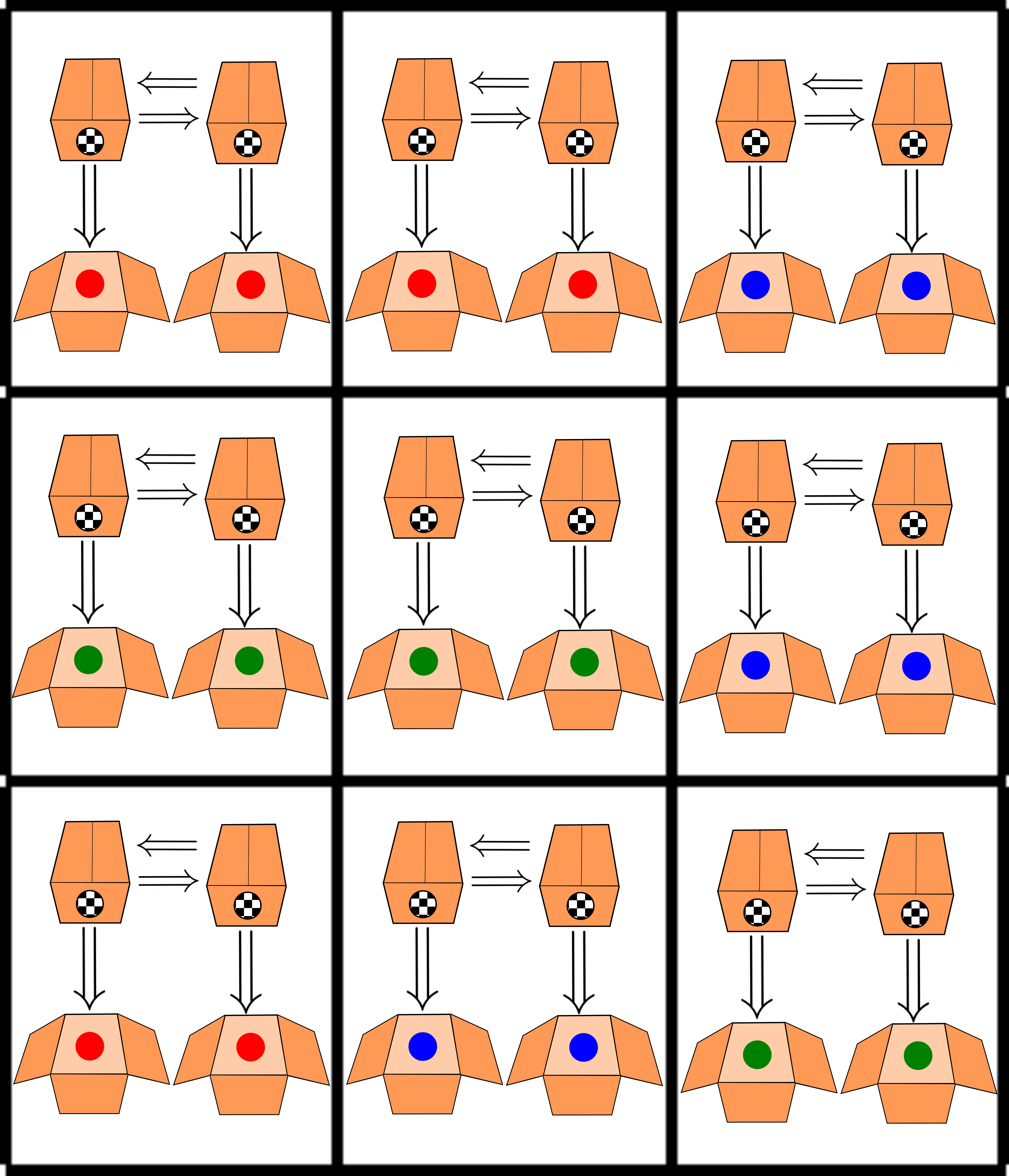
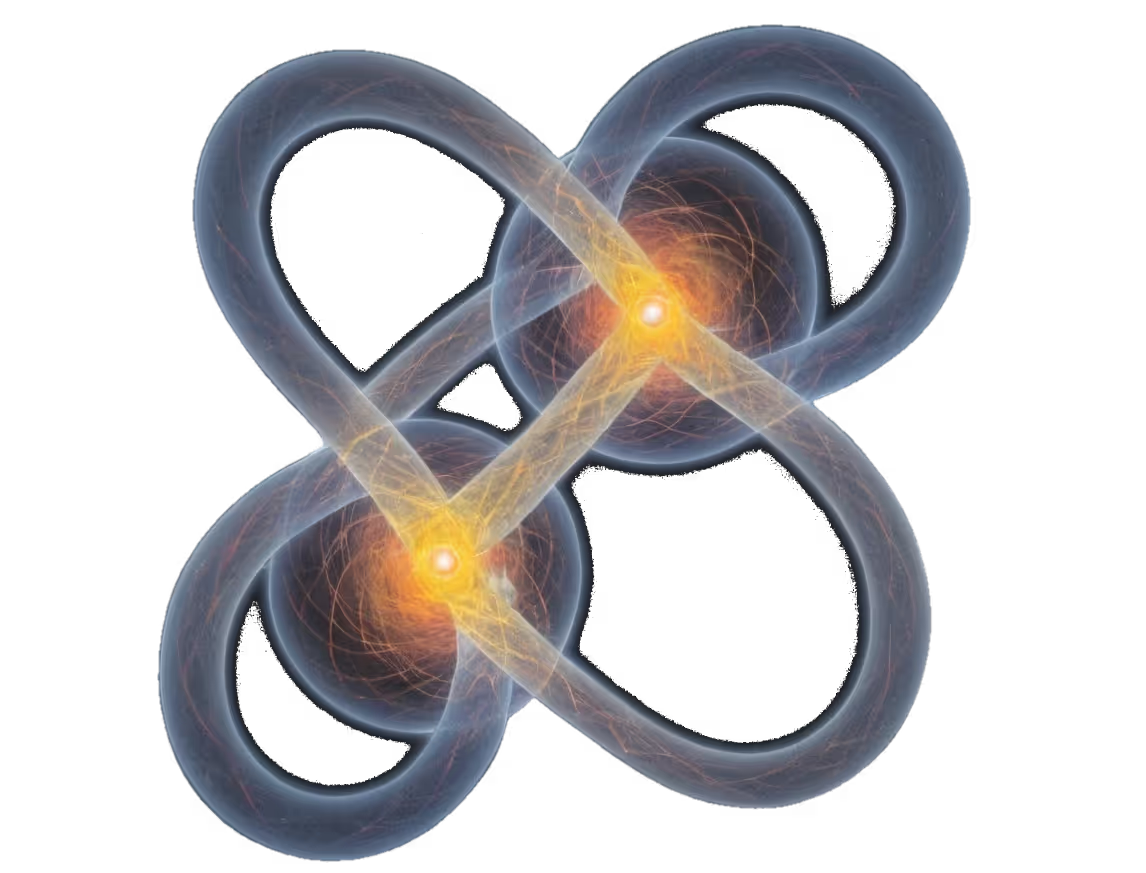
Now consider two boxes, each containing one quantum particle. The setting is the same as above, but this time, the interaction that occurred in the past can correlate the particles in a very special way called quantum entanglement, depicted below as a figure-eight-shaped loop enclosing both particles inside the boxes. This strong form of correlation is ideally assumed to remain intact until we look inside the boxes. Once we look inside the boxes (the act of measuring), entanglement is destroyed. What remains is a conventional relation: both particles have the same color.
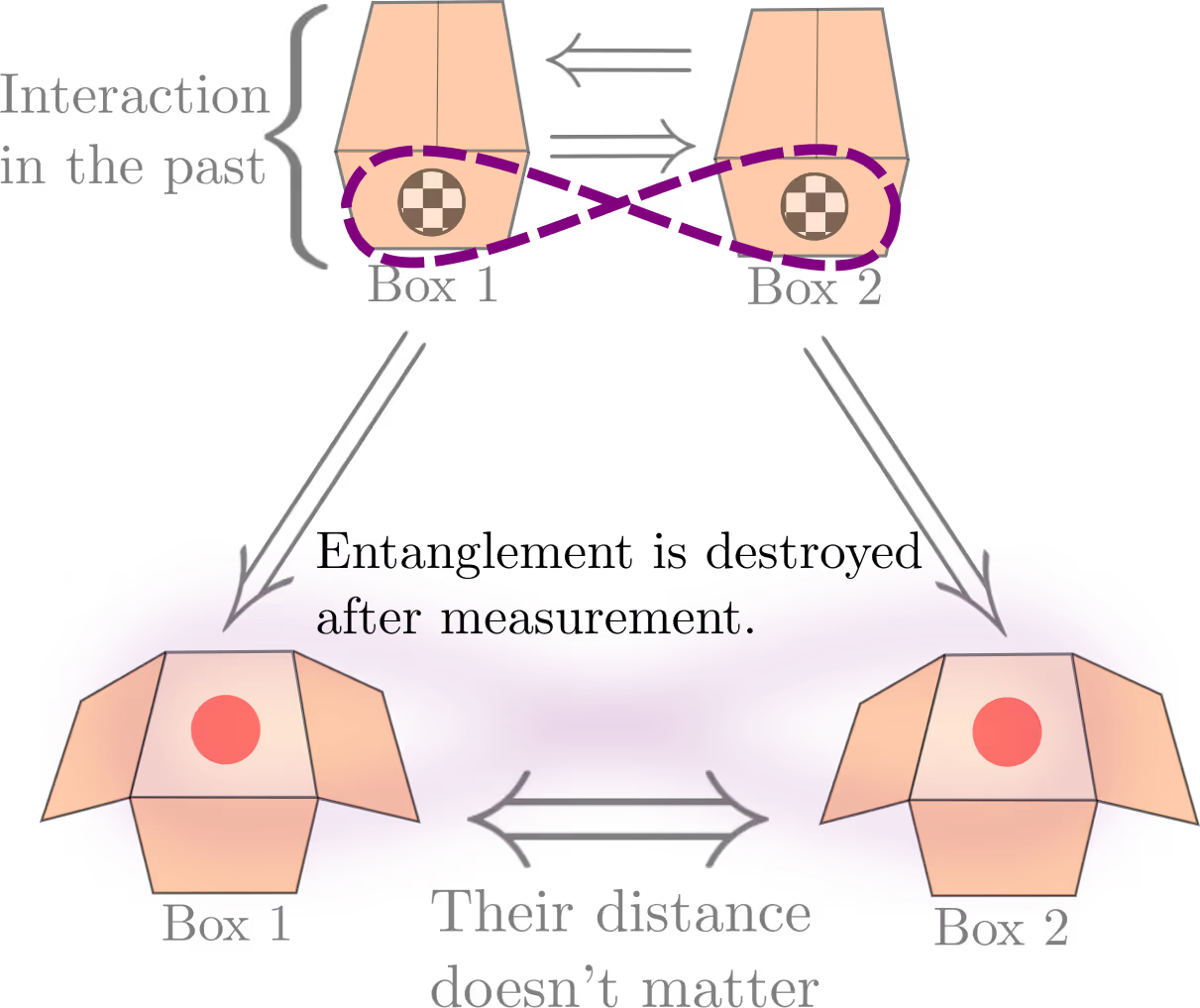
This is the same setup as shown earlier, but here the balls represent quantum particles that are entangled, depicted by a figure-eight-shaped loop.
The Mechanism Behind
Quantum entanglement is a type of quantum correlation, in fact, it is the strongest example. Moreover, it is a direct and beautiful consequence of the superposition principle. In the setting above, the quantum system is conformed of two particles. If we stick for a moment to conventional probability theory, we can imagine that the system can be in many combinations (if we consider three colors, they are 9 combinations), for example:

But wait! we are interested only in correlated outcomes, so let us stick only with three combinations:
Such combinations are enough to describe conventional correlations, the interaction in the past fixes the color of both balls and that’s it. Now, quantum mechanics allows also superpositions, therefore, the interaction can produce also quantum states with the form.
These type of states are called entangled states. They are regarded as special for many reasons:
Factorization.— When two particles are entangled, their quantum state is determined only globally, this is, we need the big picture to realize that there is a quantum superposition somewhere (after all, the superposition involves both particles). When this happens, we say that the state cannot be factorized, meaning that it cannot be understood as two particles individually holding separate colors:
⇒ If you are familiar with conventional probability theory, this “non-factorizability” is analogous to having two correlated random variables, a and b, where their joint probability distribution cannot simply be expressed as the product of their marginals: P(a, b) ≠ P(a)P(b).
If we need to measure both particles to realize that there is entanglement, what happens if we have access to only one of them?— Interestingly, as mentioned above, we cannot observe the entanglement in action when we only have access to one particle. What we see is the conventional situation discussed earlier: the particle has a determined color prior to measurement; we just don’t know it until we observe it. In other words, there’s no trace of quantum superposition, and the system appears entirely conventional.
Spooky action at a distance.— In the early days of quantum mechanics, the prediction of quantum entanglement sparked considerable criticism among some of the greatest minds, including Albert Einstein, who famously referred to it as “spooky action at a distance” (EPR paradox). Einstein was troubled by the idea that something appeared to be transmitted instantaneously between entangled particles, which seemed to violate the discoveries of special relativity. To understand why this was so perplexing, consider the following scenario: if the two boxes containing the entangled particles are far apart—say, separated by a vast distance like the diameter of our galaxy—measuring the state of one particle immediately determines the state of the other, regardless of the distance between them. This phenomenon is a consequence of the collapse of the wave function. Finding one particle to be red means that the other particle, far away, must also be red, as dictated by the initial superposition. Thus, the process unfolds as follows:

This is because the only option where one particle is red is when both of them are red!
This instantaneous correlation challenges the classical idea that information can’t travel faster than the speed of light, which led to Einstein’s deep concerns about the predictive power of quantum mechanics. However, in the EPR paradox paper, Einstein and his colleagues introduced important ideas that shaped our understanding of reality in physics. Although they incorrectly concluded that quantum entanglement didn’t fit these ideas, we now know that entanglement not only exists but also aligns with fundamental principles that any solid physical theory should uphold.
Quantum Entanglement Is a Resource
It’s important to note that the exotic properties of quantum entanglement do not imply that faster-than-light transmission of information or matter is possible. However, quantum entanglement is still a valuable natural phenomenon that can be harnessed as a resource to power novel technologies based on the quantum behavior of matter. One such application, which sounds straight out of science fiction thing, is quantum teleportation. Another groundbreaking application is quantum computing, where entanglement is a key ingredient that enables quantum bits (qubits) to perform complex calculations at speeds unattainable by classical computers. These technologies, once theoretical, are now at the forefront of research and development, paving the way for a new era of computing and communication.
In this post we will discuss quantum teleportation.
Quantum Teleportation
Quantum teleportation often sparks a range of misconceptions. Some envision it as a magical trick that simulates teleportation, while others imagine it involves traveling faster than light or operating at breakneck speeds. The truth is, quantum teleportation is far from science fiction—it’s a profound concept deeply embedded in quantum mechanics. Though it can seem mysterious and complex, diving into its nuances reveals an incredible potential for revolutionizing communication and computation. Far from being just a fantastical idea, quantum teleportation is a real and exciting frontier in the quantum world, poised to change how we think about information and technology.
The Teleportation Protocol
To understand how quantum teleportation works, let’s first consider the hardware involved (see the image below). Imagine a telecom company providing two quantum channels—perhaps high-quality optical fibers—connecting Alice(A) and Bob(B) to a source of entangled photons. Each of them receives one photon from the entangled pair. The device is perfectly synchronized, so Alice and Bob know they hold complementary halves of the same entangled pair. Alice’s task is to communicate a series of qubits to Bob using quantum teleportation, with one qubit being teleported per entangled pair.
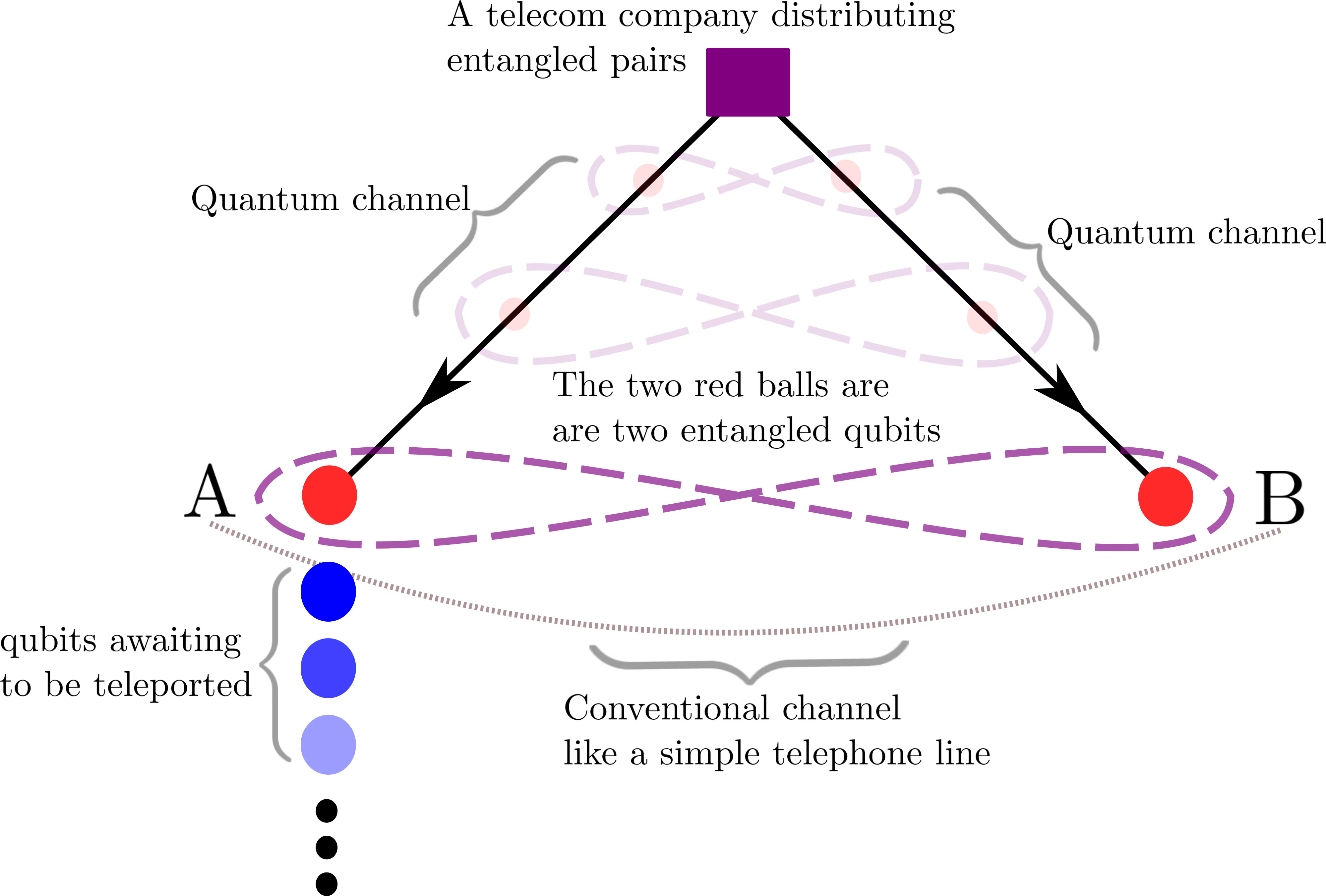
In addition to the quantum channels, Alice and Bob also need a conventional (classical) communication channel. This classical line is crucial for completing the protocol.
Protocol Steps
The quantum teleportation protocol is inspired by the fact that after measuring entangled pairs, Alice and Bob can compare their results to confirm the entanglement. Instead of merely comparing results, they leverage this entanglement to complete the teleportation process. Essentially, they assume the entanglement is present and use a process akin to “comparing the results” to transfer the quantum state to Bob’s particle. This might sound complex, but let’s break it down into a few clear steps:
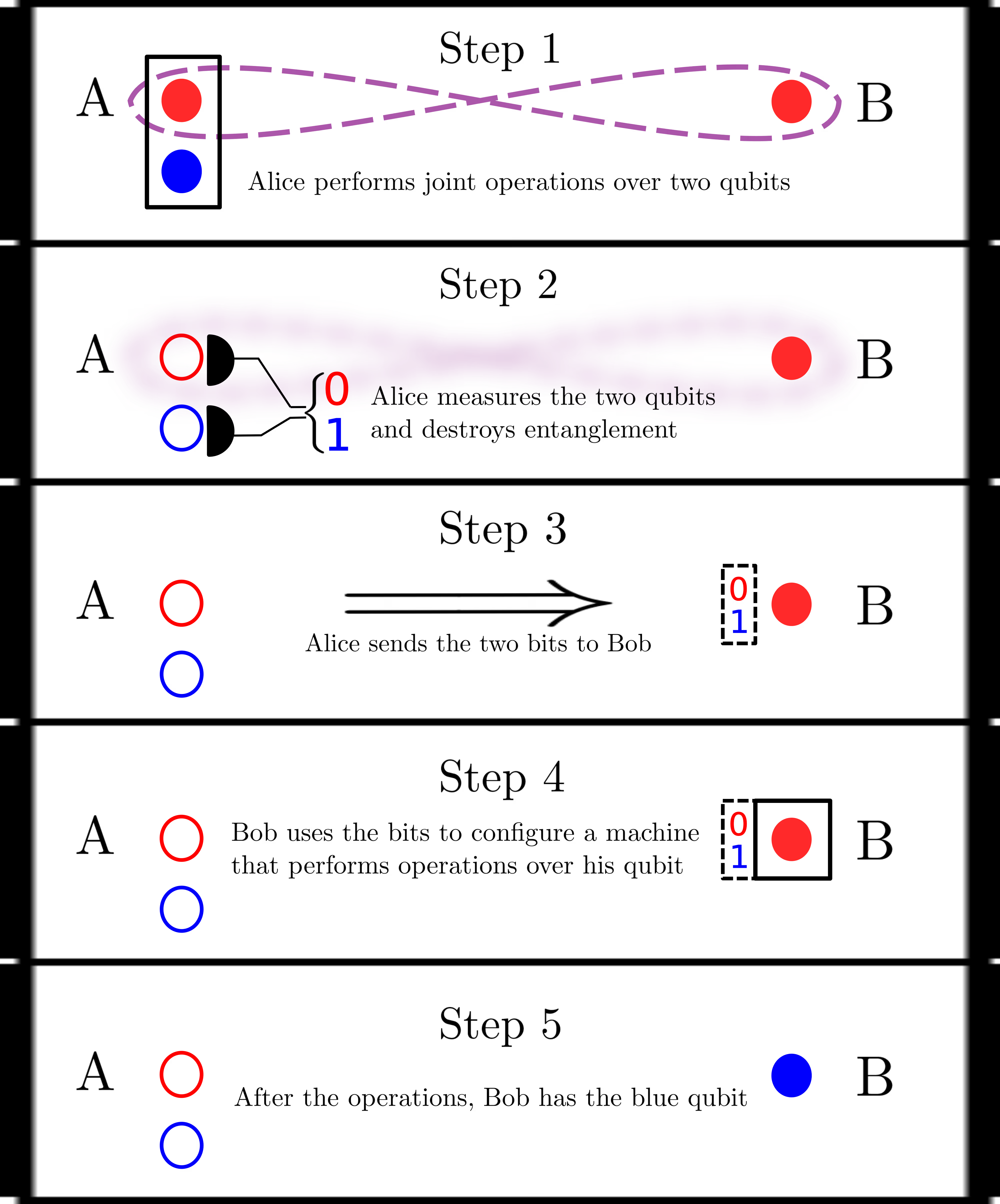
- Preparation: With the entangled pair in place, Alice performs joint operations on both qubits—her end of the entangled pair and the qubit she wishes to teleport. This is possible because the qubits are physically close together.
- Measurement: Alice then measures both qubits, which can result in one of four possible outcomes: 00, 01, 10, or 11. This measurement causes both qubits to collapse, which also leads to the disappearance of entanglement and leaves only conventional correlation between Alice’s results and Bob’s qubit.
- Classical Communication: Alice sends the results of her measurements to Bob via a classical channel, such as a telephone call.
- Operation Configuration: Bob uses the information received from Alice to adjust the operations he performs on his own qubit.
- Completion: After Bob completes these operations, his qubit will be in the state that Alice intended to communicate.
So, What Happened? Was the Qubit Really Teleported?
This is a natural question because, after all, some classical information is communicated between Alice and Bob. How can we call this process “teleportation”? — Before delving into the details, it’s important to note that a qubit cannot be constructed from just the two bits Alice sends to Bob. A qubit is described by two real numbers, which means it requires infinitely many bits to be written (or at least a very precise approximation using for instance two floats of 64 bits, this is, 128 bits). Therefore, these two bits do not hide the qubit. What happens is that when Alice performs operations on her two particles, entangling them, and then measures them, she instantaneously creates correlations between the qubit she wants to send and the particle Bob has. However, Bob doesn’t know the precise form of these correlations until Alice sends him the two bits from her measurement.
Moreover, the bits generated during the protocol are independent of the qubit Alice wants to send—they are entirely random. This leads to some interesting observations:
- No information is being transmitted through the quantum channels; they merely provide entangled pairs with no inherent information.
- The conventional communication lines used to send the bits do not transmit any meaningful information either, as these bits are random.
Putting these two aspects together leads to a mind-blowing conclusion: the quantum information (the qubit) is not transmitted in any conventional sense—it literally disappears from its original location and reappears in Bob’s location! However, this isn’t as magical as it might seem; bear in mind that the qubit is information, not a piece of matter. The atom that originally held the qubit is still there, but the information has been teleported to Bob’s particle.
Applications of Quantum Teleportation
Quantum Computing
Quantum teleportation is not only a groundbreaking concept but also a natural and reliable method for communicating quantum information, even over short distances, such as within the registers of a quantum computer or its quantum RAM. Its key advantage lies in the fact that the required hardware only needs to be tuned to reliably communicate entangled pairs, rather than being engineered to transmit any quantum state directly.
Quantum teleportation is also crucial for transmitting quantum information over long distances, which will be particularly valuable for connecting quantum computers in a network. While it’s possible to use quantum channels directly to send information, these channels are not perfect, and quantum information could be incredibly valuable. A practical model of quantum computing envisions multiple quantum computers, each optimized for specific tasks, working together. In such a setup, quantum information, which may be the result of complex and costly computations, is highly valuable.
Of course, long distances can also affect the entangled pairs used in teleportation. However, challenges like these are addressed with innovative solutions, such as the quantum repeater—but that’s a story for another time.
Quantum Cryptography and Quantum Communication
As you may have noticed, since quantum information is not physically transmitted from Alice to Bob, quantum teleportation naturally lends itself to cryptographic applications. Quantum teleportation allows for the secure transmission of both classical and quantum information. The crucial point is that the information isn’t traveling through any medium or cable—making it inherently un-interceptable!
This scheme, together with quantum encryption protocols such as quantum key distribution whose functioning basics are explained in our previous post under the name basic example of quantum encryption, provides encryption schemes robust against quantum encryption-breaking devices. Nowadays, most used encryption schemes rely on the fact that in order to break the key, a very hard mathematical problem must be solved.
An example of this is prime number factorization, which the RSA protocol is based on. These schemes rely on the fact that it is easy to multiply two prime numbers to generate the key, such as 3 and 5, getting 15; but factoring any number in its prime factors is hard. Ok, probably with 15 it is not that hard, but think about very big numbers, those are the ones used in modern encryption.
Such types of encryption can be broken with a fault-tolerant quantum computer (although quantum computers already exist, fault-tolerant ones are still waiting to come into existence) using Shor's algorithm, which is able to factorize prime numbers in a polynomial time (meaning a reasonable time increasing with respect to the size of the input number), instead of the most efficient classical algorithm, which runs in sub-exponential time (a very bad increasing with respect to the size of the input number).
Since quantum encryption algorithms do not rely on hard mathematical problems but in the quantum nature itself, they are naturally robust against Shor's algorithm.
Final Word
Quantum entanglement is at the heart of the ongoing second quantum revolution, paving the way for next-generation quantum devices and new communication schemes. Notably, the concept of a quantum internet is becoming a reality through various global initiatives, including those in China, Slovakia, Czechia, Hungary, and Austria, Tokyo’s QKD Network, and SwissQuantum. These networks aim to enhance existing communication infrastructure by adding a quantum layer on top of the current internet. While many of these networks initially focus on quantum key distribution for secure communications, they also hold potential for groundbreaking applications like blind computing, secure position verification, leader election, and more.
Despite the uncertain pace of development and the varying popularity of these technologies, we anticipate that they will soon become viable commercial alternatives. At Austin Ai, we are committed to staying ahead of these technological shifts and preparing for the evolving landscape of quantum technologies.